The information below provides the baseline configuration for NC State’s Jamf Pro environment to meet the control requirements of the Endpoint Protection Standard.
All NC State Jamf Pro administrators must implement these baseline controls in their Jamf Pro Site.
If a group is not able to meet these controls, an IT Exception must be submitted to Security & Compliance via this exception request form.
As always TEST policies and profiles on a small group of devices before deploying them to an entire Site.
Note that other helpful documentation about setting up Apple device management in Jamf Pro can be found at go.ncsu.edu/jamfcheat.
Quick Index
Endpoint Protection Standard RUL 08.00.18 – Endpoint Protection Standard
AntiMalware/Antivirus
Application Control
Authentication
Encrypted Network Communication
Full Disk Encryption (with key escrow)
Host-based Firewall
Least Privilege Access
Software Inventory
Web Reputation Filtering
Patch Standard RUL 08.00.14 – System and Software Security Patching Standard
While not strictly part of the Endpoint Protection Standard the University Patch Standard must be implemented at as a complete defense against threats on university data.
macOS Patching
AntiMalware/Antivirus
Use a Jamf Policy to install DetectX as a supplement to Apple’s XProtect.
Two policies are needed to ensure proper install and scanning.
Full documentation is on the DetectX Setup for Jamf Pro page.
Authentication
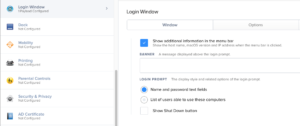
Use a Apple Configuration Profile in Jamf Pro to ensure that the Login Window option has setting for:
1) Window tab is set to show Name and Password Fields for the Login Prompt as in Figure 1.
2) Options tab is set to Disable Automatic Login as in Figure 2.
Apple Kerberos Single Sign On Extension
Additionally use a Jamf Configuration Profile to enable the built-in Apple Kerberos Single Sign On Extension(SSOE) provided with every macOS devices running 10.15 or newer. This built-in security feature of macOS will keep the local account password in sync with the campus WOLFTECH directory. See:
https://docs.google.com/document/d/1ZRdpM1atzSsITfGFSRYCQTcLajnfznr8mbAeZR98Uz8/edit?usp=sharing
Host-based Firewall
Use a custom Apple Configuration Profile that enables the Firewall and enables Stealth Mode. In Jamf Pro upload into the Configuration Profiles tab the custom profile that manages just the firewall preferences in the com.apple.security.firewall preference domain from
While Jamf Pro does have a Security & Privacy Option payload, setting just the Firewall in this option locks out the management of other important settings from user control. The by uploading the custom profile only the needed settings are locked.
Least Privilege Access
Meeting this control is simply setup methodology where accounts are not created with full administrative access to the device. In macOS, Apple allows creation of Administrator, Standard, and Sharing Only accounts. Creating new users with the account type Standard will meet the control. Commonly you will hear complaints from end users that this does not allow them to install software. The intent of this control is to protect the data stored on the device NOT to keep software from being installed! In today’s world software can be run from external storage like key drives or even directly downloading to the home directory and running from there where no extra permissions are required. Best practice for software installation is the direct clients to use Jamf Self Service.app as no elevation of permissions are needed. If software installation permissions are needed these can be granted using the authorization database without giving full administrative access.
To allow installation of software only create a Jamf policy which configures the Files and Processes Option to have an Execute Command of:
/usr/bin/security authorizationdb write system.install.software <<< $(/usr/bin/security authorizationdb read system.install.software | /usr/bin/sed 's/admin/staff/g')
This uses the security command line tool to read the system.install.software rule in the authorization database replace the value of the group setting with the group staff and write it back again. All users are in the staff group and this will not interrupt the builtin Apple install mechanisms nor those used by configuration management. To verify that this worked use the command line:
/usr/bin/security authorizationdb read system.install.software
And look for the group key:
<key>group</key> <string>staff</string>
Note: Standard Users will still have to type in their username and password to complete the install but admin permissions are not required.
For situations where full administrative access is actually the least privilege required, time limited privilege elevation can be granted using the Privileges.app from https://github.com/SAP/macOS-enterprise-privileges The installer for Privileges.app is available in the campus configuration management system. Read the documentation for setup as there are several options.
Software Inventory
When an Apple device is enrolled into the campus configuration management system (Jamf Pro) a software inventory is automatically collected and updated on a daily basis. Some policies also update the device inventory after running. To force the inventory to update use the jamf command line tool in Terminal.app to run: /usr/local/bin/jamf recon
Web Reputation Filtering
This control is met by installing and patching modern web browsers such as Safari or Google Chrome since these browser vendors have built in safeguards against known bad browsing sites.
Application Control
Deny Application Execution
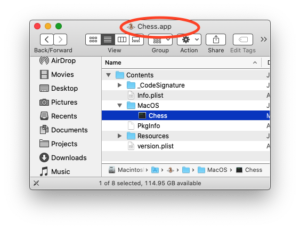
Use the Jamf Pro Restricted Software feature to set restrictions on applications that are not allowed to run by the process name. Using the process name means that moving or renaming the app will not circumvent the control. In Jamf under the Computers tab, click on Restricted Software in the side bar and add a new restriction. Here we will restrict the Chess.app game from running.
First we need to find the process name by viewing the contents of the application bundle. Right clicking on the Chess.app icon in the Applications folder and selecting “Show Package Contents” using the Finder will show the application’s bundle contents. Look in the Contents folder inside the MacOS folder as shown:
Once we have the correct process name “Chess” we can complete the restriction as shown:
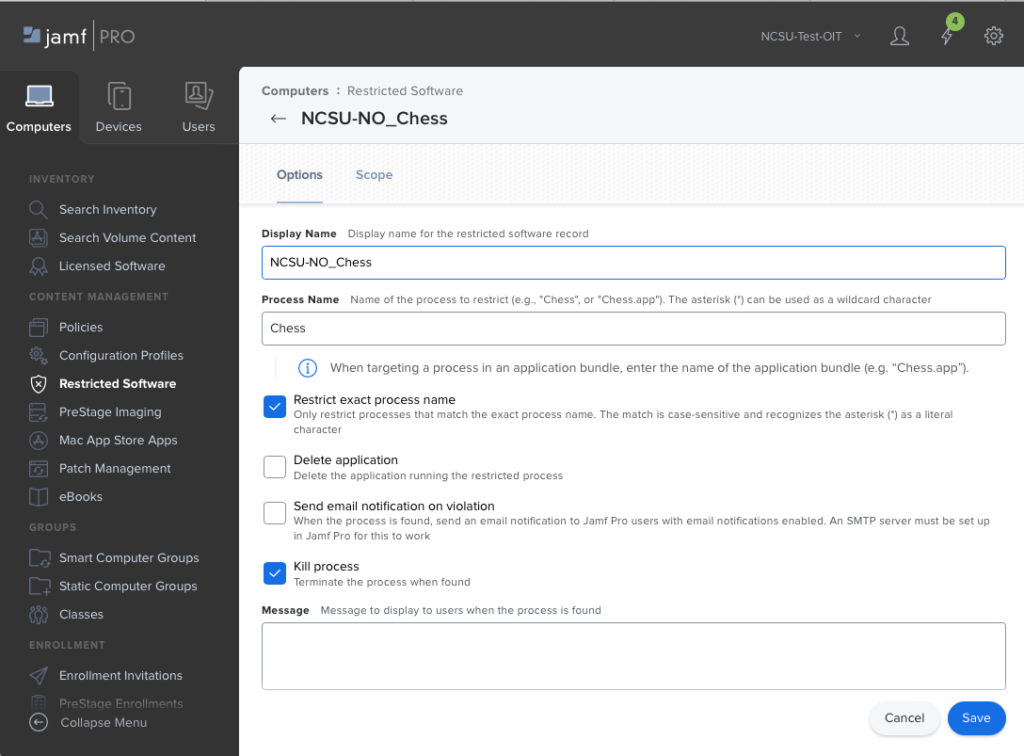 Fill out the Display name with something descriptive, put the exact, case sensitive process name in the Process Name field and check at least the Kill process box. One may choose to have the application Deleted, and/or send email on violation. A restriction must be made for each application process to be denied. Be aware that some applications may have frameworks and libraries that are not removed by the Jamf Delete Application option and an uninstaller from the vendor or a custom script may be needed for complete uninstall.
Fill out the Display name with something descriptive, put the exact, case sensitive process name in the Process Name field and check at least the Kill process box. One may choose to have the application Deleted, and/or send email on violation. A restriction must be made for each application process to be denied. Be aware that some applications may have frameworks and libraries that are not removed by the Jamf Delete Application option and an uninstaller from the vendor or a custom script may be needed for complete uninstall.
Allow Application Execution
Use a macOS Configuration profile with the Parental Controls: Application Access (id: com.apple.applicationaccess.new) payload to create an allow list for applications that can run. Download the NCSU-Allow Applications-Template.mobileconfig file that can be modified with Profile Creator.app to add the desired apps. When desired applications are added just use the Upload button in the Configuration Profiles side bar of the Computers tab in Jamf Pro to import and scope.
Other Considerations
Be aware that there are other methods that could be used to allow or deny application execution.
Apple requires all applications to get permission to use certain resources on a device. These resources are called entitlements and they can be denied using various profiles mostly associated with the Security & Privacy System Preferences panel. While none will deny applications running, they can deny access to entitlements like Full Disk Access, Files and Folders, etc in a way as to make the app unable to access data rendering it useless.
Here are some additional resources:
Apple Profile Documentation
https://developer.apple.com/documentation/devicemanagement/parentalcontrolsapplicationrestrictions
3rd Party workflow for Blocking Apps
https://derflounder.wordpress.com/2017/05/20/application-blacklisting-using-management-profiles
Using GateKeeper to create allow/deny lists
https://apple.stackexchange.com/questions/313373/block-specific-apps-on-macos
Encrypted Network Communication
Part of meeting the Encrypted Network Communication control of the Endpoint Protection Standard is to make it as easy as possible to use the eduroam encrypted network available on campus and at supporting institutions around the world. To do this create a Jamf configuration profile that uses device certificates to automatically join our eduroam wireless network.
- Use the side bar under the Computers tab to select Configuration Profiles and create a new profile using the +New button.
- In the General option give the profile a descriptive name, description, and leave Distribution Method set to “Install Automatically”.
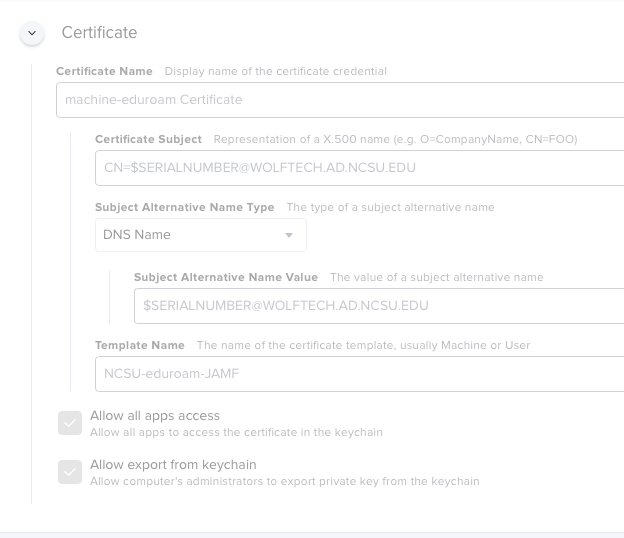
- Select the Certificate option and configure to add 3 certificates.
- Name the first Certificate “NCSU-Device-Eduroam” or something appropriate
Use the Select Certificate Option drop down to pick “North Carolina State University Root CA256-RSA”
Set the Certificate Subject to “CN=$SERIALNUMBER@WOLFTECH.AD.NCSU.EDU” NOTE: this must be exact and case matters
Set the Subject Alternative Name Type to “DNS Name” from the drop down.
Set the Subject Alternative Name Value to “$SERIALNUMBER@WOLFTECH.AD.NCSU.EDU” NOTE: again must be exact and case matters
Set the Template Name to “NCSU-eduroam-JAMF” NOTE: yes again must be exact and case matters!
Finally check the box for “Allow all apps access” but leave “Allow export from keychain” unchecked - Use the + button to add a second certificate by uploading a copy of the InCommon RSA Server CA.cer from
https://drive.google.com/file/d/1EcwQbNT_c4SiF_d2qUuWTa-dpbnmhBSq/view?usp=sharing Note: login required to download.
Name the certificate InCommon RSA Server CA or something appropriate. Leave the passwords blank and leave all check boxes as configured. - Use the + button to add a 3rd and final certificate “North Carolina State University Root CA256-RSA” by uploading
https://drive.google.com/file/d/1eljlWE3nngEqMQw4e2sbZkVD0BS7cM2D/view?usp=sharing Note: login required to download
Name the certificate North Carolina State University Root CA256-RSA or something appropriate. Leave the passwords blank and leave all check boxes as configured.
- Name the first Certificate “NCSU-Device-Eduroam” or something appropriate
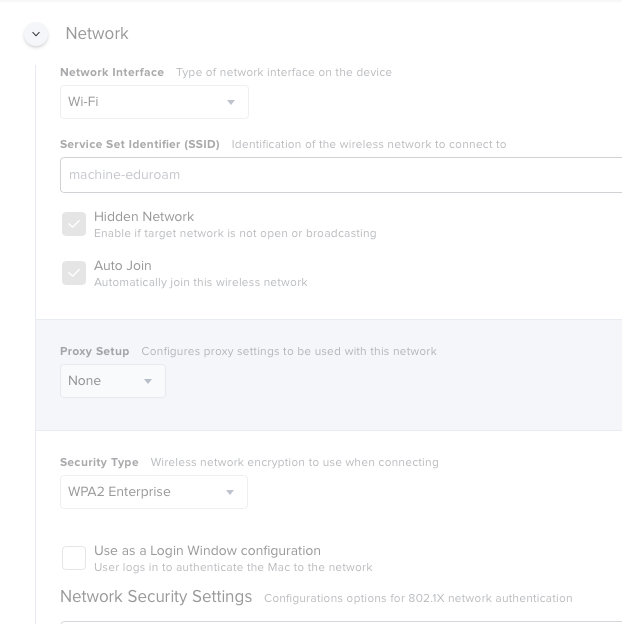
- Now the Certificate option is finished and a Network option in this same profile must be configured
- Select the Network option from the side bar and configure the Network Interface to WiFi checking the Hidden Network and Auto Join options
- Set the Service Set Identifier (SSID) to “eduroam”
- The Proxy should remain as None
- Set the Security Type to “WPA2 Enterprise” from the drop down menu.
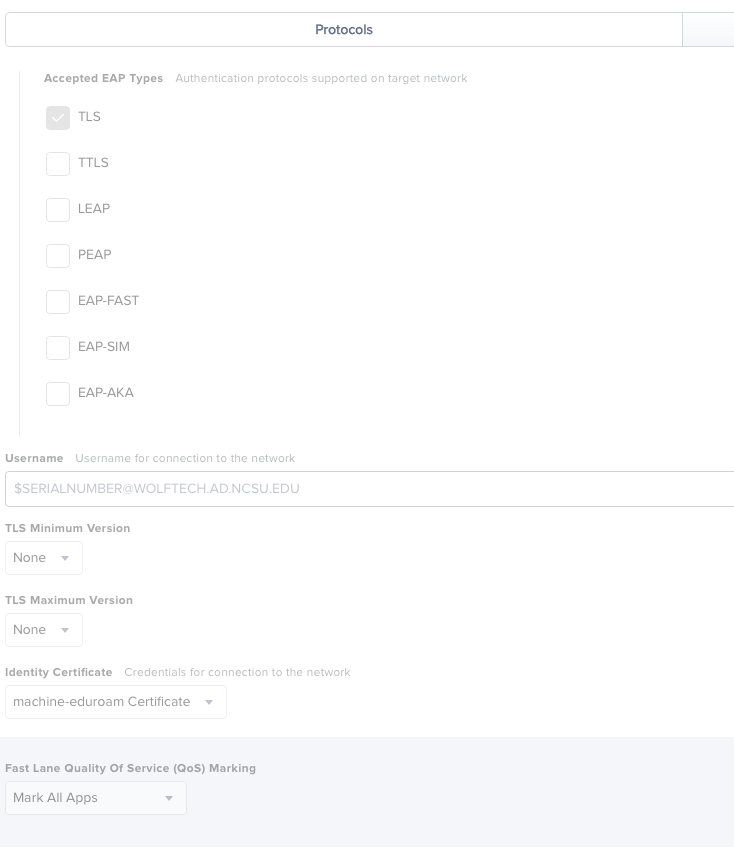
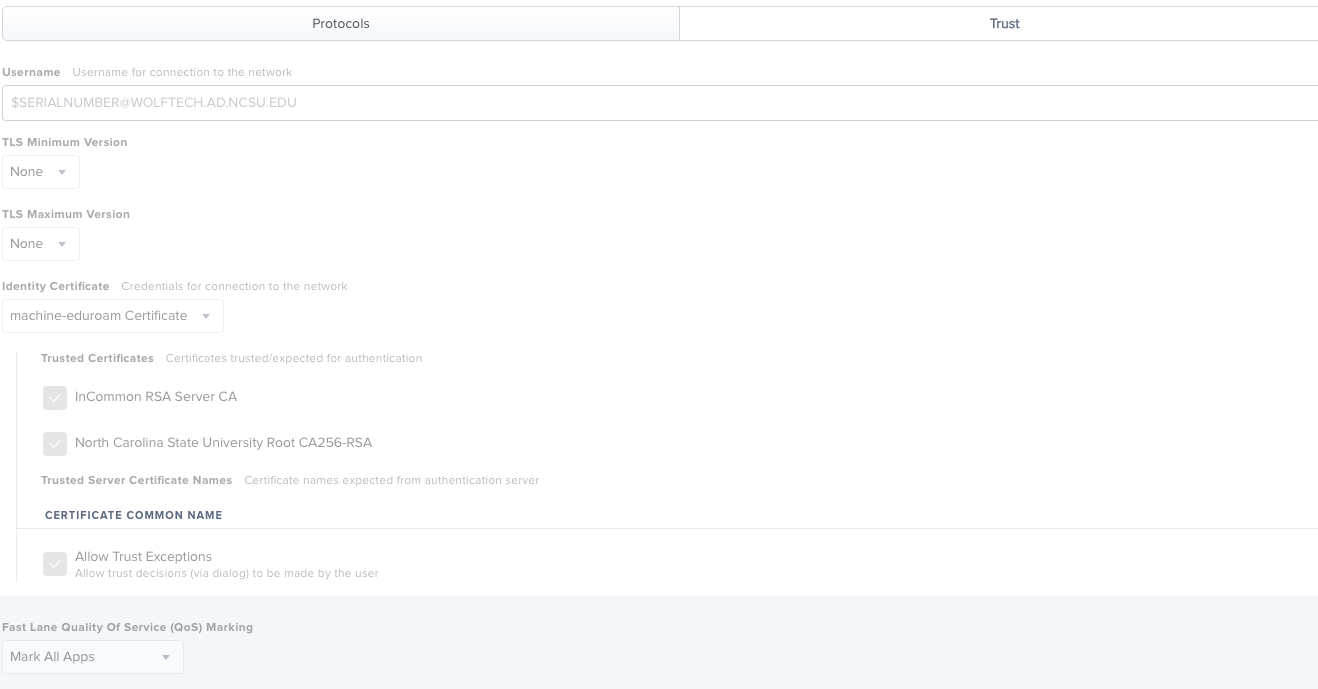
- Under the Protocols tab select TLS check box
- Set the User Name to “$SERIALNUMBER@WOLFTECH.AD.NCSU.EDU” NOTE: must be exact and case matters
- Now select the Identity certificate as “NCSU-Device-Eduroam” ( or the name you gave the first certificate created earlier).
- Leave everything else default and select the Trust tab and make that the Username and Identity Certificate are the same as on the Protocols tab.
- Next under Trusted Certificates check the boxes beside the other 2 certificates uploaded earlier: InCommon RSA Server CA and North Carolina State University Root CA256-RSA to have macOS automatically trust them for all users in the KeyChain. This is so the client will not see a dialog asking for them to be approved when the profile installs.
- At the bottom check Allow Trust Exceptions
Finally scope and save the profile as desired.
See these screen shots for example profile settings:
Full Disk Encryption
The easiest way to meet this control is to edit the template custom configuration profile for Apple’s FileVault2 encryption:
Template-NCSU-Campus-FileVault2.mobileconfig from
https://drive.google.com/file/d/1Ev5S0ZHIjTUhGyCgHhO35u0ynVK7nD4s/view?usp=sharing
with Profile Creator, signing it, and uploading it to our configuration management system (Jamf Pro). The template profile manages only the FileVault 2 settings and does not lock other setting in the Security & Privacy system preferences panel. This profile has been tested on macOS versions 10.15.0 and newer and may not work on earlier OS versions. Note: Most Apple devices use flash storage with APFS volumes and not spinning hardware disks. This is important when off-boarding encrypted devices for surplus as they should be cryptographically erased for best data security.
Considerations -Please Read
Usernames who can decrypt the storage volumes on device startup is limited to a) usernames created with either the Setup Assistant or b) usernames created with the Users & Groups system preference panel. These usernames have what is called a Secure Token allowing them and only them to decrypt the disk. To be clear usernames that are network users (like most <UNITY>.admin accounts), local accounts created with NoLoAD, sysadminctl, or Jamf policies will not be able to decrypt the disk without manual work. The template profile is setup to escrow the recovery key which can be used to decrypt the disk both for login and disk repair and will require a password change when used. For devices managed using the configuration management system (JAMF Pro) and running macOS 10.15.3 or newer on devices with the T2 security chip, another encryption key is saved called the Boot Strap token. This Boot Strap token should be used by the configuration management system to grant usernames created using policies Secure Tokens allowing them to decrypt the data volumes.
For versions of macOS before 10.15.x, other methods maybe needed to escrow keys or grant secure tokens to usernames. Best practice is to upgrade all devices to macOS 10.15 or newer. Several of these posts provide great information and guides to working with FileVault2 on earlier versions of macOS: https://derflounder.wordpress.com/category/filevault-2/
Patch Standard – macOS Patching
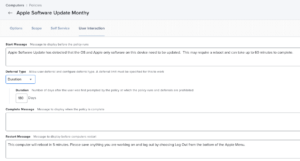
1) Offering Apple software updates to the end user allowing them to defer updates. This is the best way to entice your end users to patch with out disrupting anything critical (teaching, video conferencing, etc) they might be doing. This is the preferred way of setting up patching.
Use a monthy Jamf Pro policy with a Software Updates option where Allow Deferral has been allowed in the User Interaction tab. Note that in Jamf Pro version10.21.0 and beyond deferral can be configured for a number of days or a specific date. Best practice is to use day based deferral when possible. It is also best practice to enable this policy for Self Service so clients can update as they please to get better compliance.
2) Forcing an update regardless of what the user is doing.
This is not polite nor kind, will forcibly disrupt whatever the client is doing, and will cause data loss, interruption of presentations, teaching, video conferencing, etc.
Also note that Apple has indicated this may change in macOS beyond 10.15.x
Use a Jamf Pro policy with a Files and Process option to run Apple’s command line software update tool. Use the install and all command line switches
/usr/sbin/softwareupdate --install --all
in the EXECUTE COMMAND field to install all macOS updates. NOTE: with 10.14 and beyond this will not install updates to App Store apps as it did with earlier versions. See figure for example of Jamf Policy.
On macOS 10.13 and beyond Apple software updates can be forced even at the Login Window by using the SoftwareUpdateLauncher instead:
/System/Library/CoreServices/Software\ Update.app/Contents/Resources/SoftwareUpdateLauncher.app/Contents/MacOS/SoftwareUpdateLauncher" -RootInstallMode YES -SkipConfirm YES
3) To force a major macOS update or update to a specific version
On macOS 10.15 or newer use a Jamf Pro policy with a Files and Process option to run this command:
/usr/sbin/softwareupdate --fetch-full-installer --full-installer-version 10.15.7 && '/Applications/Install macOS Catalina.app/Contents/Resources/startosinstall' --agreetolicense --forcequitapps --nointeraction
This command would upgrade (but not down-grade) to version 10.15.7 of macOS. If you need to **destroy all the data on the device**, format the boot volume, and start over add these switches to the command:
--eraseinstall --newvolumename 'Macintosh HD'
With macOS 11.0+, authentication as a local administrator account is required to force a silent, unattended macOS install. The command is
/usr/sbin/softwareupdate --fetch-full-installer --full-installer-version “11.1” && /usr/bin/su -l <localadminuser> -c "echo <localadminpass> | /Applications/Install\ macOS\ Big\ Sur.app/Contents/Resources/startosinstall --nointeraction --agreetolicense --forcequitapps --user <localadminuser> --stdinpass"
Again to do complete Erase and Install add
--eraseinstall --newvolumename 'Macintosh HD'
Of course the version of macOS desired and the actual admin user and password should be substituted(angle brackets<> are not needed). Be aware that this may not work if the device is at the login window with no user session and a local account with administrative privileges must exist(tho one could create a local admin, run the command and then remove the admin).