To protect university assets, OIT S&C develops and publishes the following types of documentation to assist the campus community with meeting compliance obligations:
NOTE:
At NC State University, information security standards are developed and published as rules.
About PRRs
OIT S&C develops PRRs working collaboratively with all campus IT representatives. Upon final approval, OIT S&C then works with the Office of General Counsel (OGC) to publish the PRRs in the Information Technology category of the university’s Policies, Regulations & Rules (PRR) website.
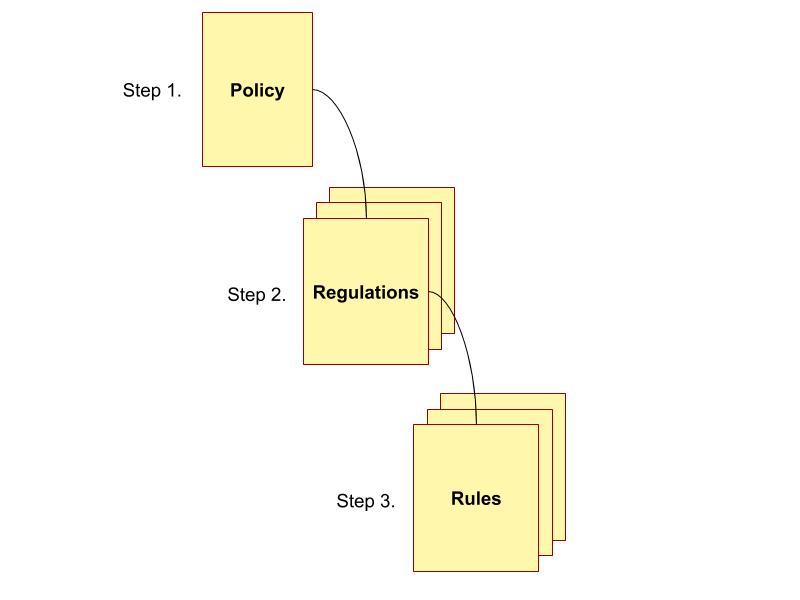
Before establishing any regulations or rules, a policy must exist. Regulations support the policy with details about general applicability, while rules provide details relevant to specific circumstances.
NOTE: After developing and publishing a complete PRR set, OIT develops and publishes supplemental guidance, which typically consists of one or more documents or web pages providing detailed, step-by-step instructions.
See the following sections for details:
- PRR Definitions
- PRR Development
- PRR Review and Approval Process
- Published PRRs
- Supplemental Guidance
PRR Definitions
OIT S&C adheres to the university’s PRR definitions defined in Table 1.
Table 1. PRR Definitions
| PRR Type | Governing Body | Definition |
| Policy | Adopted by the Board of Trustees pursuant to authority delegated by law or the Board of Governors. | Any standard, statement, or procedure of general applicability |
| Regulation | Adopted by the Chancellor or chancellor’s delegee. | Any standard, statement (which may include a policy statement), or procedure of general applicability |
| Rule | Adopted by an academic or administrative unit within the university to implement an NC State University Policy or Regulation; alternately, can address matters within the operational authority of the unit. A Rule may supplement, but not conflict with, policies and regulations. | A standard, statement or procedure, other than a policy or regulation |
PRR Development
In conjunction with all UNC System institutions, and per the Chancellor’s Adoption Letter dated March 2012, NC State University adopted ISO 27002, an internationally recognized framework for information security. The ISO 27002 Security Framework guides the development of OIT S&C PRRs.
PRR Review and Approval Process
After creating or revising the first draft of a PRR, the draft undergoes the review and approval process defined in the following IT PRR Process flowchart and Table 2:
IT PRR Process flowchart:
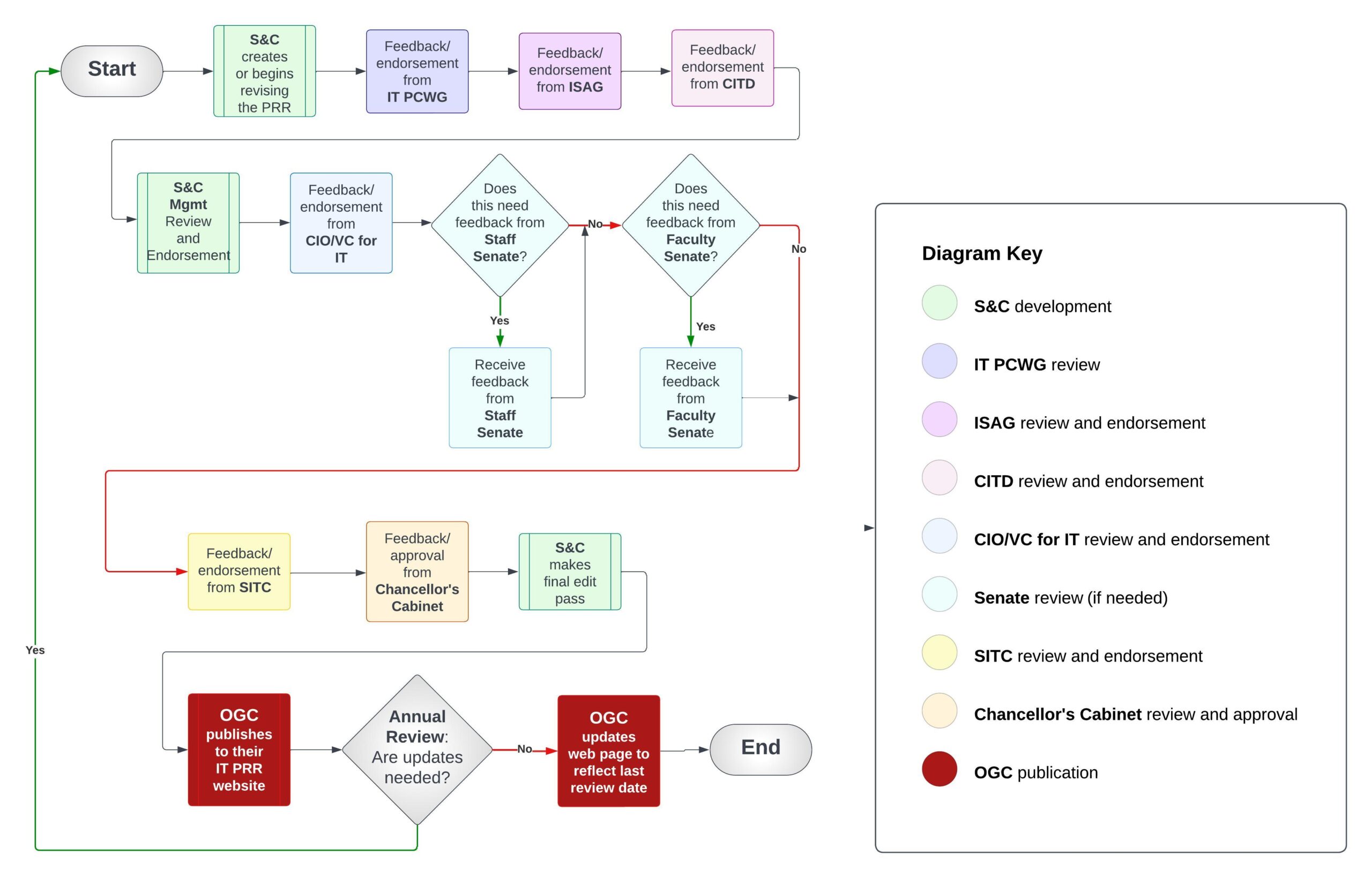
Table 2. PRR Review and Approval Process
| Step | Action Owner | Description |
| 1 | Information Security Advisory Group (ISAG) | Review and endorsement |
| 2 | Appropriate IT governance structure and other committees as needed | Review and endorsement |
| 3 | Chancellor’s Cabinet | Review and approval |
| 4 | Office of General Counsel (OGC) | Publish to PRR website |
Published PRRs
OIT S&C works with the NC State Office of General Counsel (OGC) to publish formally approved PRRs to the university.
The following PRRs are published on the university OGC website:
Computer Use Policy
is the Computer Use Policy for NC State, which defines university IT, user responsibilities, and consequences for violating the following:
- Federal and state laws
- University policies and procedures related to the use of IT
Computer Use Regulation
is the Computer Use Regulation, which supports the Computer Use Policy and further defines the following:
- University IT
- User responsibilities
- Consequences for violations
Data Management Regulation
assigns responsibility for the custody and security of university data.
- Applies to all university data and computing systems (both administrative and user-developed) that access or use university data
- Governs management and accessibility of university data regardless of the environment where the data resides
Antivirus Software Requirements Regulation
prescribes antivirus software requirements to protect the campus computing infrastructure.
Network Printer Security Standard
helps the users of NC State Networked Printers protect sensitive university data should a device become compromised, lost or stolen.
Vendor-specific security measures may be appropriate for some devices.
System and Software Security Patching Standard
outlines the minimum requirements for applying security patches, updates, and fixes, aka “patches.”
This standard applies to information system components:
- Including but not limited to firmware and BIOSes, operating systems, applications, and services connected to the NC State network
- Used to process, store, or transmit NC State data
NC State University Security Standards for Sensitive Data
and Systems
complies with REG 08.00.02-Computer Use Regulation and ensures appropriate security protections are in place.
Provides guidance for protecting the university’s sensitive data:
- Ultra-sensitive (purple data)
- Highly sensitive (red data)
Cybersecurity Incident Response Procedure
provides detailed plan and procedure to respond effectively to a cybersecurity incident at NC State, whether impending or active.
Endpoint Protection Standard
is the Endpoint Protection Standard, which outlines the minimum security requirements for all desktops, laptops, smartphones, tablets, etc. that access or store university data.
Supplemental Guidance
In addition to publishing PRRs for the protection of university data, OIT provides the supplemental documentation described in this section.
Password Standard
NC State’s password standard complies with REG 08.00.02 (the Computer Use Regulation) to ensure appropriate security protections are in place; defines the password requirements at NC State and applies to anyone accessing the NC State network.
Mobile Device Security
In accordance with the Computer Use Regulation and RUL 08.00.18 — the Endpoint Protection Standard (EPS), the Mobile Security at NC State website provides detailed procedures to secure the mobile devices, data, and wireless connections of all campus members who use them to access university data. These guidelines apply to university personnel using mobile devices to access any university data, including email. In addition, these guidelines help secure that data should a device become compromised, lost, or stolen.
Technology for Travel
The Technology for Travel page provides requirements and tips for securing mobile devices before, during, and after traveling. When you travel with a laptop, tablet or smartphone, the risk of loss and theft are so much higher — losing not only your device but also the data it stores.
Please note it is impossible to protect mobile devices against every form of data breach; however, the more you do, the safer you are.
EPS Guidance
The EPS Guidance page helps IT support staff comply with security requirements per RUL 08.00.18 — the Endpoint Protection Standard (EPS). All IT groups are responsible for complying with said EPS requirements per their areas of responsibility.
Example of PRR and Guidance
The following figure shows how RUL 08.00.18 — the Endpoint Protection Standard (EPS) and the EPS Guidance page correlate to the earlier PRR hierarchy figure.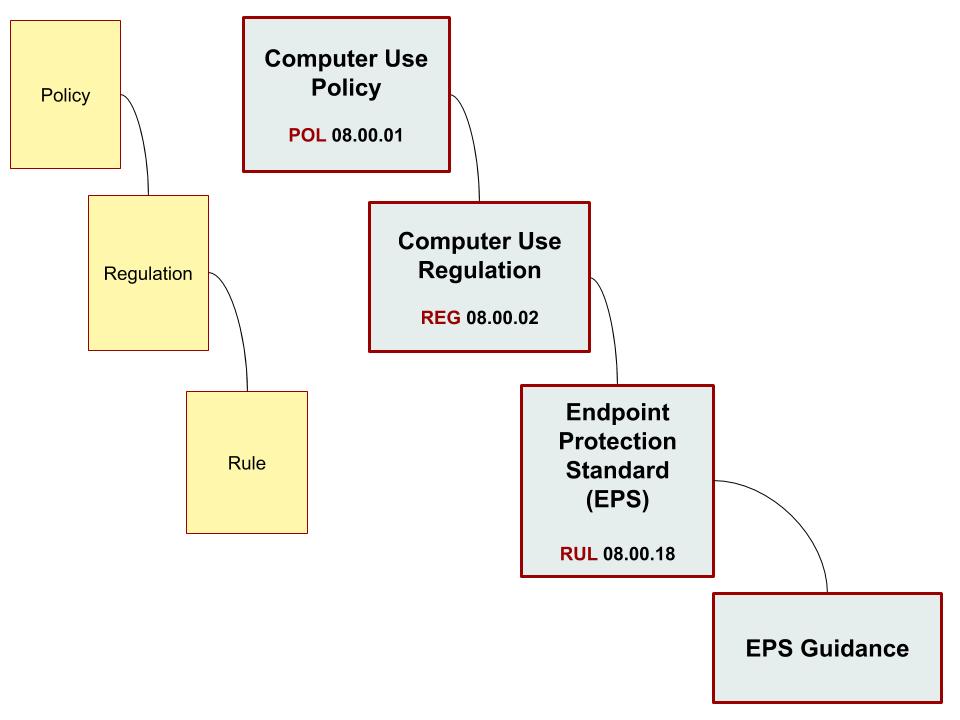
Next Page
| Home | Previous | Next |
| Information Security Program at NC State | Compliance Assurance | Cybersecurity Awareness and Training |